JKS Trust Store
If you require LDAP authentication, it is necessary, in order to connect to the Confluent Schema Registry via a secure connection, to select the SSL type. A keystore contains client certificate and client key. Whereas a truststore contains certificate authority (CA).
There are different ways to leverage the Java Keystore (JKS):
- Keystore info only: if the server doesn’t need truststore, the application assumes that client certificate is the certificate authority. The application retrieves the client certificate and key from the keystore, and uses certificate as CA.
- Truststore info only: if the server doesn’t require a keystore, but requires a truststore, then the application takes only the certificate authority from the truststore, and connects without client certificate and key
- Both keystore and truststore: if the server requires both a keystore and a truststore, then the application takes the certificate authority from the truststore, plus the client certificate and key from the keystore.
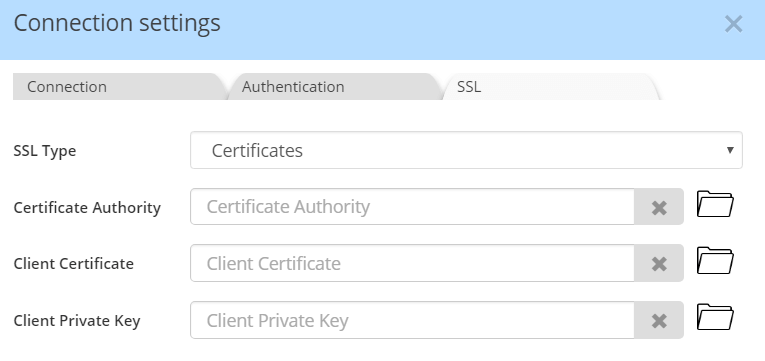
Alternatively, you may use certificates issued from the keystore.
Accessing the keystore
Specify the path and filename to keystore, the access password, and the alias name for the Confluent Schema Registry instance.
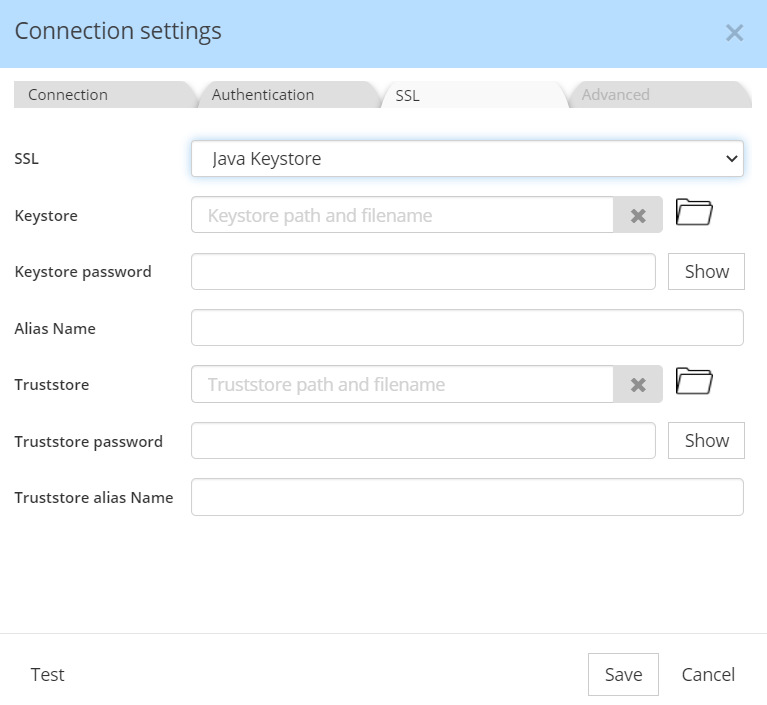
The Alias Name is mandatory. If you don't know it, it can be found out by the following command:
keytool -v -list -keystore <jks file>
The alias can be found in the section “Alias name”. If no alias was set, you should use the default "mykey".
Accessing the truststore
If necessary, you may also declare truststore parameters:
You may consult this page for more info, as well as the full keytool specification.
Accessing both the keystore and the truststore
Enter the parameters according to both 1) and 2) above.
Convert the keystore and truststore into PEM keys
Assuming cassandra server config (cassandra.yaml):
client_encryption_options:
enabled: true
keystore: keystore.jks
keystore_password: *******
truststore: truststore.jks
truststore_password: ******
require_client_auth: true
-
Install java if you don't have it: https://www.java.com/en/download/
-
Install openssl: https://wiki.openssl.org/index.php/Binaries
- Linux: sudo apt-get install openssl
- MacOS: brew install openssl
- Windows: https://slproweb.com/products/Win32OpenSSL.html
-
Find out alias used by keystore
Run the following command to find out what alias is used by keystore:
> keytool -v -list -keystore keystore.jks
where keystore.jks is the java key store file granting access to the cassandra instance
alias will be in the section “Alias name”
- Generate PKS key
> keytool -importkeystore -srckeystore keystore.jks -destkeystore myapp.p12 -srcalias myapp-dev -srcstoretype jks -deststoretype pkcs12
keystore.jks - the java key store file granting access to the cassandra instance
myapp.p12 - intermediate PKS key
myapp-dev - alias used by keystore and determined in step 3 above
5. Generate CA key
> keytool -importkeystore -srckeystore truststore.jks -destkeystore trust.p12 -srcalias myapp-dev -srcstoretype jks -deststoretype pkcs12
6. Generate .pem key
> openssl pkcs12 -in myapp.p12 -nokeys -out myapp.pem
> openssl pkcs12 -in trust.p12 -nokeys -out ca.pem
> openssl pkcs12 -in myapp.p12 -nodes -nocerts -out myapp.key
7. Use generated files in Hackolade:
“Certificate Authority”: ca.pem
“Client Certificate”: myapp.pem
“Client Private Key”: myapp.key